Now that our Amazon API Gateway is up and running it is crucial for us to detect any errors or misusage. Our Lambda functions already have logging enabled by default and we can see the possible errors and usage metrics under each function’s Monitor tab. On the other hand, our API Gateway doesn’t have logging enabled by default. In this episode, we will set up logging for that as well.
CloudWatch settings
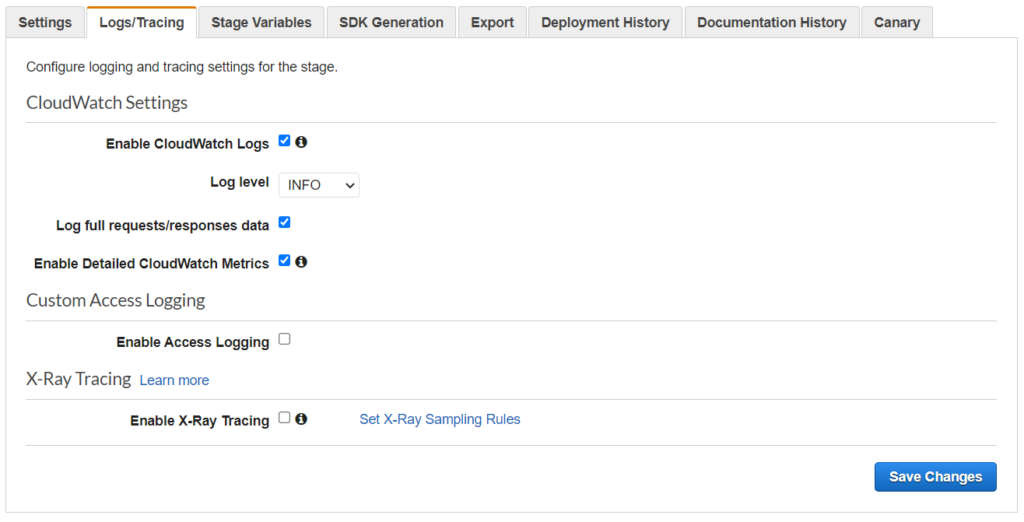
Different logging settings can be applied for each API stage. That is why we find the CloudWatch settings under Stages -> [stage name] -> Logs/Tracing.
For CloudWatch logs we can select from two logging levels: INFO to generate execution logs for all requests or ERROR to generate execution logs only for requests that result in an error.
We have the option to log full requests/responses data by selecting the appropriate checkbox.
Also here we can enable detailed CloudWatch metrics.
Let’s say we have never enabled API logging before. In this case, when trying to save our changes we will get the following error:
CloudWatch Logs role ARN must be set in account settings to enable loggingCloudWatch permissions
The above error appeared because we have not yet set up the CloudWatch log role ARN under Settings.
❗ Keep in mind that API settings are global. They apply to all of our gateways. Changing the CloudWatch log role ARN in one API Gateway will change it on all of our gateways provided that we are using the same region!
Let’s try adding our previously created role: simple-api-role ARN. You get the ARN from the IAM console -> Roles, and then selecting simple-api-role.
Upon adding our ARN we get another error: 🤯
The role ARN does not have required permissions configured. Please grant trust permission for API Gateway and add the required role policy.Our role is not yet configured to write to CloudWatch. Let’s go back to IAM and update our simple-api-role with the proper permissions.
First, we need to attach the AmazonAPIGatewayPushToCloudWatchLogs policy to our role. We have done adding policies to roles before. If you have stuck go back to the Adding a new Lambda function to an API Gateway post where I described how to attach a new policy to an existing role. But we are not done yet… ⏱️
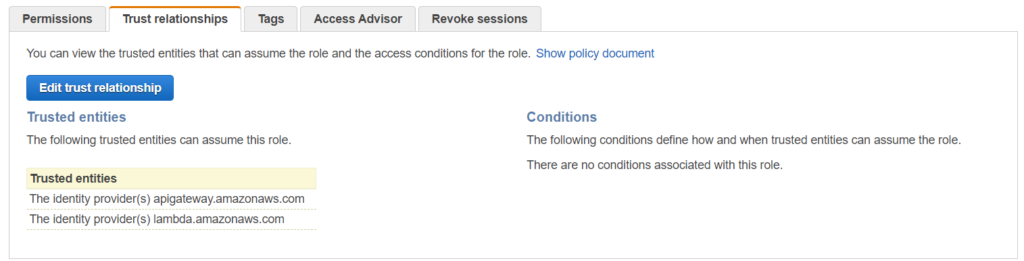
On the Trust relationships tab click Edit trust relationship and add apigateway.amazon.aws.com. If you only used Lambda with this role this example policy document will work for you:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"Service": [
"lambda.amazonaws.com",
"apigateway.amazonaws.com"
]
},
"Action": "sts:AssumeRole"
}
]
}Now that the permissions are properly configured we can go back to the API Gateway and add the role without any errors. 🤠
Finish
We have set up the CloudWatch log role ARN now it’s time to enable logging in our API Gateway.
When we enable logging in the /aws/apigateway/welcome log group we will see a new log entry: Cloudwatch logs enabled for API Gateway. This means we have done a great job! 🥳 Unfortunately, the log message doesn’t say for which gateway but based on the timestamp we can double-check if this our gateway.
The Amazon API Gateway will generate a new log group based on the following format: API-Gateway-Execution-Logs_apiId/stageName. Here we can find the log entries for our API Gateway.
We are almost finished with our API Gateway series. But we have the most important task to last: Documentation. 📄
